The Architecture
The Trust Stack
The verification architecture that makes truth automatic. A living system that makes identity, intent, authenticity, and provenance instantly verifiable across every artifact, workflow, and transaction.
Replaces assumptions with proof
Replaces risk with certainty
Replaces trust-by-belief with trust-by-design
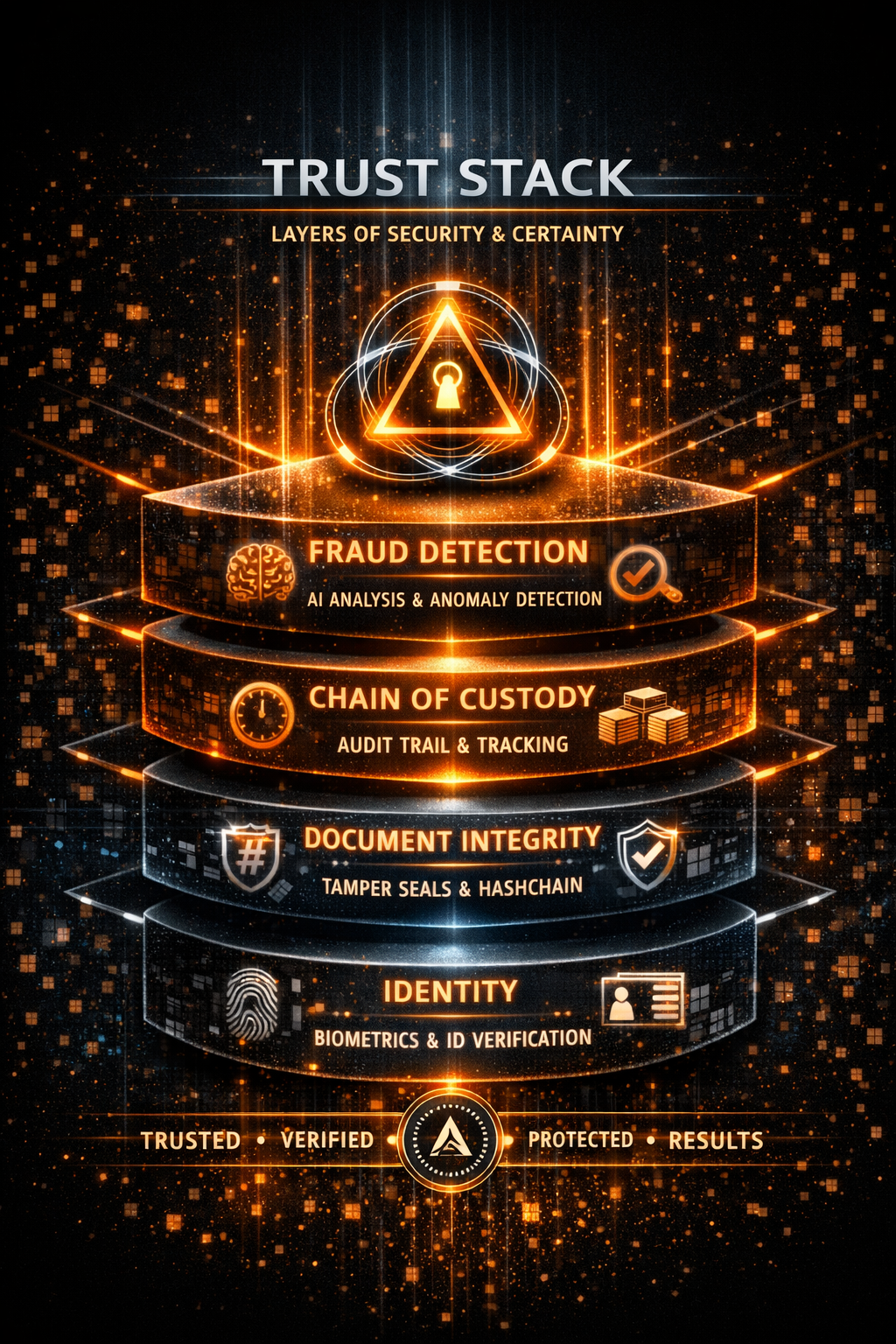
The Four Core Layers
Four Layers.
One Truth.
Together these layers form a civilization-grade trust system. Each layer strengthens the next. The full stack eliminates fraud at the origin.
-
Confirms the three things every enterprise must know before accepting any action. This is the first moment enterprises realize: "This system understands people, not just data."
Identity — who is acting
Intent — what they meant to do
Authorization — whether they were allowed to do it
Eliminates impersonation, coercion, and unauthorized actions at the human layer
-
The command-level verification engine. Validates every action, signature, and event with zero human interpretation. If Tri-Signature is human truth, ACP is machine truth. Together, they eliminate fraud at the origin.
Command-level logging of every action
Behavioral verification in real time
Signature integrity validation
Identity certainty at the machine layer
Zero-assumption validation
-
Binds an artifact's truth to its origin and exposes any attempt to alter it. If anything changes after sealing, the Seal reveals it instantly. This is how enterprises protect every version forever.
No silent edits
No hidden changes or version drift
No forged copies
No post-event manipulation
Instant exposure of any tampering
-
The physical-digital identity strip embedded into every artifact. It is not a QR code. It is not a watermark. It is a living identity layer that makes authenticity visible. When an enterprise sees the Micro-Vein, they instantly understand: they're dealing with the real deal.
Creator metadata and timestamps
Lineage and authority signature
ACP command log
Provenance hash
Step by Step
How the Trust Stack Works
Each step builds on the last. By Step 4, every artifact is self-verifying.
Step 01
Tri-Signature Verifies the Human
Intent, identity, and authorization are confirmed in a single event before anything moves.
Step 02
ACP Verifies the Command
Every action is validated automatically at the machine layer with zero human interpretation.
Step 03
The Forever Seal Locks the Truth
The artifact is cryptographically bound. Any tampering is exposed the moment it occurs.
Step 04
The Micro-Vein Carries Identity Forward
Every artifact becomes self-verifying — its identity travels with it, permanently.
Coverage
Anything That Needs Truth Gets the Stack
Anything that needs truth gets a Micro-Vein. Anything that needs protection gets a Forever Seal. Anything that needs verification goes through Tri-Signature and ACP.
Documents
Financial Workflows
Digital Assets
Supply Chain Items
AI-Generated Content
Physical Artifacts
Why Enterprises Adopt
The Outcomes That Matter
Human-Level Proof
Tri-Signature eliminates impersonation and unauthorized actions at the point of origin.
Permanent Provenance
The Forever Seal protects every version forever. Tampering is exposed the instant it happens.
Machine-Level Certainty
ACP validates every command without human interpretation — verification becomes automatic.
Zero Disruption
The Trust Stack overlays existing systems — no rip-and-replace, no downtime, no redesign.
Visible Authenticity
The Micro-Vein makes identity readable. Authenticity becomes a property you can see.
Operational Clarity
Teams move faster because they trust the inputs. Compliance becomes a byproduct of the system.
The Standard
"The Trust Stack is infrastructure — not software. A new trust layer, a new identity substrate, a new verification standard. This is the architecture that will define the next decade of enterprise trust."
Tri-SignatureACPForever SealMicro-Vein