case study
![A digital graphic with the title 'Run a Diagnostic on Your Origination Engine'. It includes a futuristic, holographic-style icon at the top and two sections below it: 'The Mapping' and 'The Guarantee', with descriptions about mapping high-velocity onboarding flow and providing operational guarantees. There is a button labeled '> [SCHEDULE THE 20-MINUTE ARCHITECTURE REVIEW]' beneath these sections, against a black background with technical, wireframe-style design elements.](https://images.squarespace-cdn.com/content/v1/69a78566255e652d8d100f01/3e026bcd-0d65-47a4-9378-4f402b1e70aa/big7.png)
Case Study: Tri‑Signature Verification — Establishing Constitutional Trust and Eliminating Fraud at the Origin for a Leading BNPL and Auto Finance Provider
Executive Summary Apex Lending Solutions, a fast‑scaling fintech operating across buy‑now‑pay‑later (BNPL) and auto finance, faced rising synthetic identity fraud and operational drag across its high‑volume origination workflows. After deploying Protocol One’s Tri‑Signature Verification Standard as the constitutional trust layer, Apex achieved a 92% reduction in synthetic fraud, a 68% drop in manual reviews, and a 75% acceleration in decision times—all without disrupting existing systems. Compliance became automatic. Operational clarity became the default. Tri‑Signature transformed verification from a reactive control into an absolute, human‑level proof mechanism.
Client Background Apex Lending Solutions serves consumers with limited credit histories across BNPL and auto finance verticals, processing thousands of applications daily and exceeding $2.8B in annual transaction volume. Prior to engaging Protocol One (March 2026), Apex relied on conventional KYC/AML tools and manual oversight—insufficient against the increasingly sophisticated synthetic identity attacks dominating the sector.
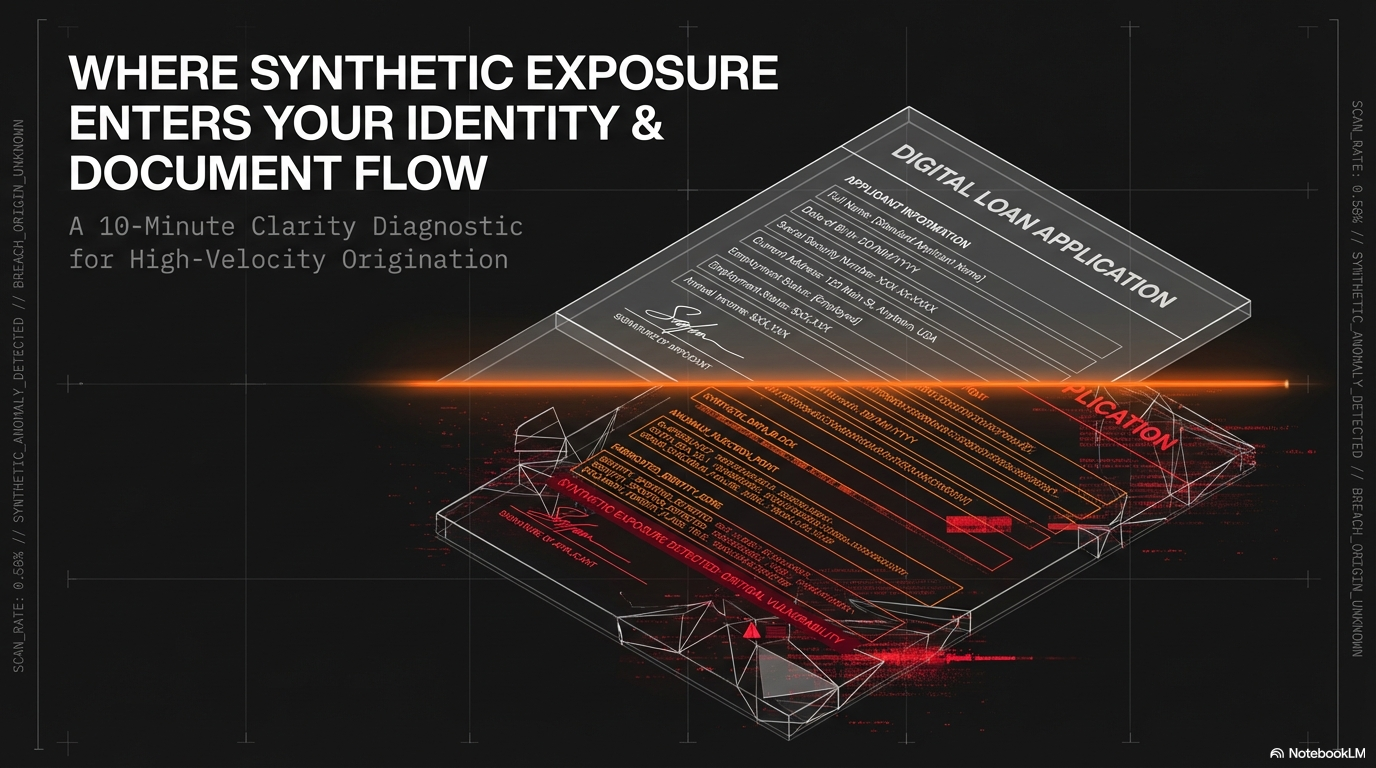
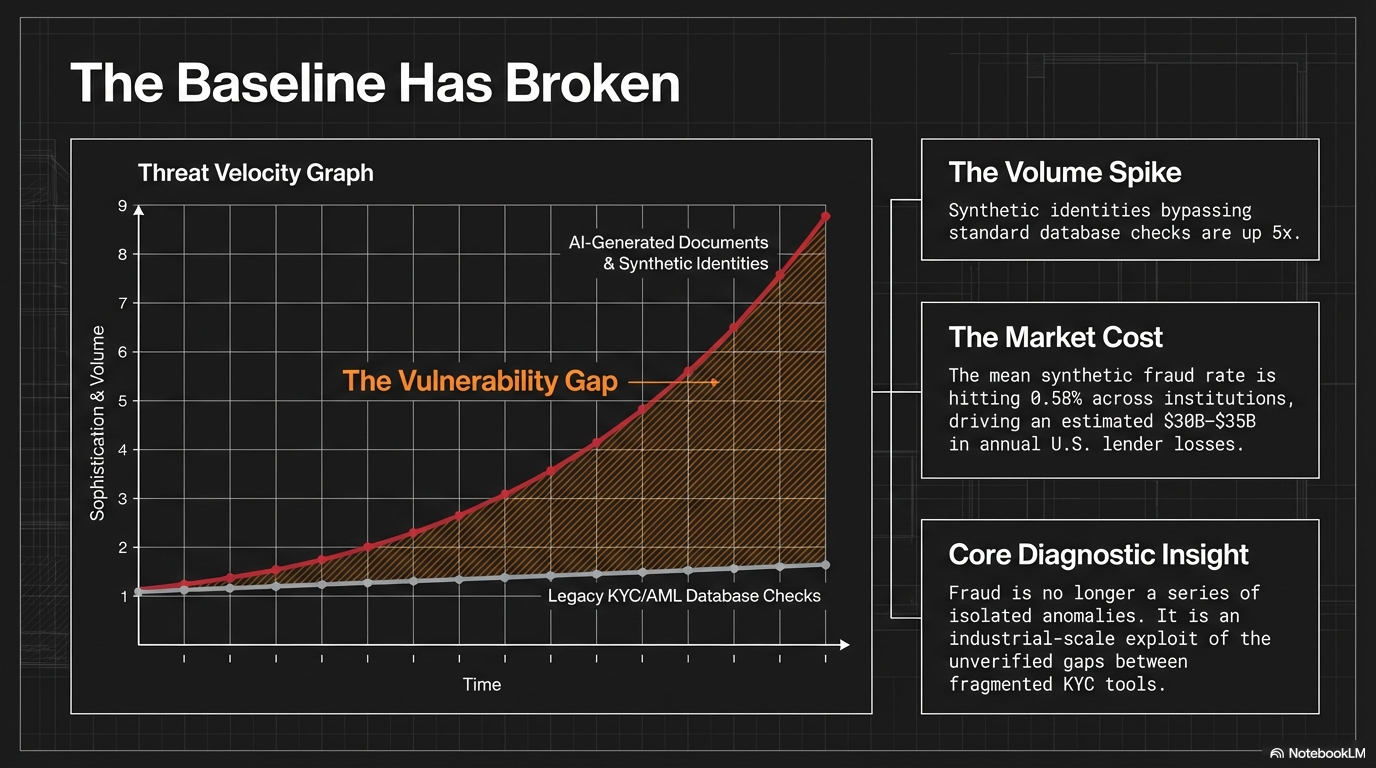
Challenges Synthetic identity fraud represents a systemic threat, with U.S. lenders facing an estimated $30–35B in annual losses and a mean synthetic fraud rate of 0.58% across financial institutions in late 2025. For Apex, this manifested as:
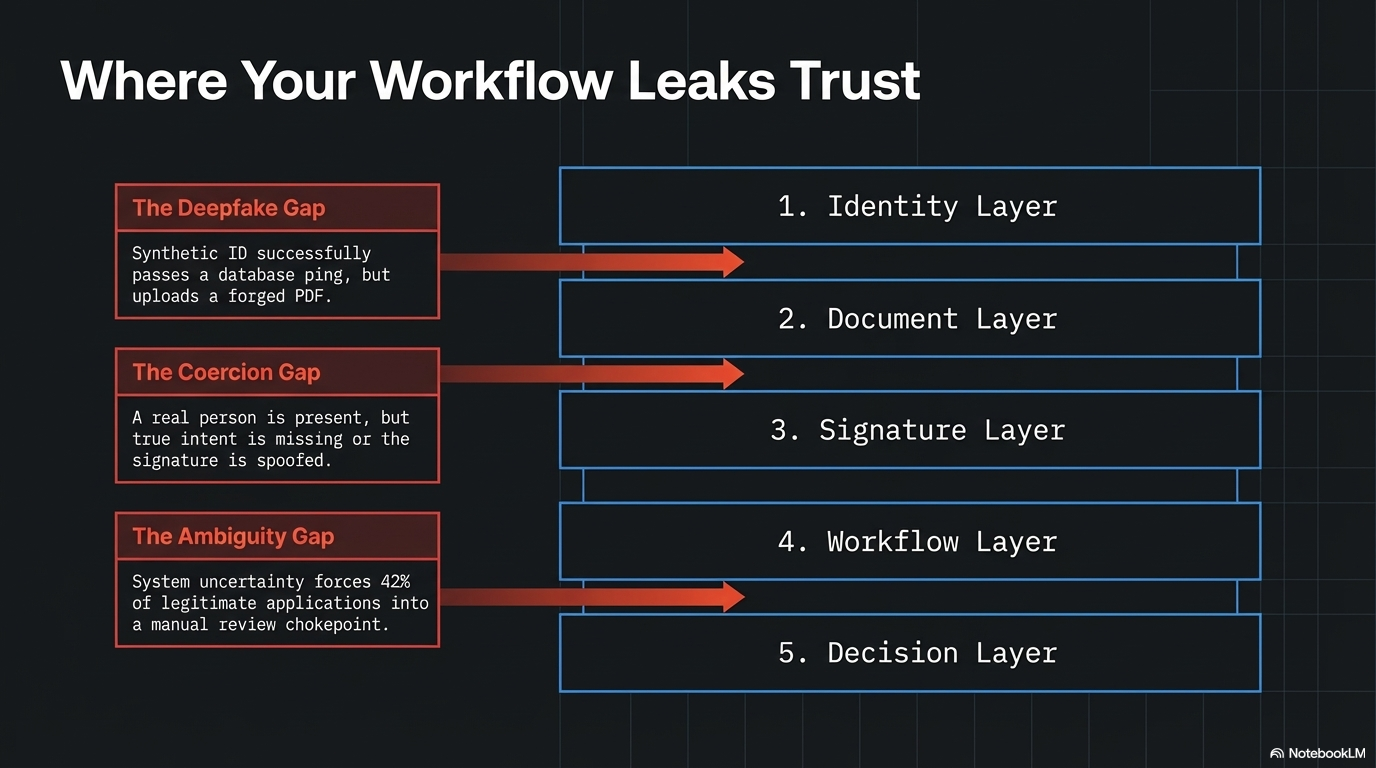
Fraud losses consuming 4.8% of originated volume, driven by synthetic identities bypassing database checks
42% of legitimate applications routed to manual review due to excessive false positives
No mechanism to confirm real‑time human intent, exposing the firm to coercion and unauthorized delegation
Increasing regulatory pressure as BNPL fraud sophistication surged year‑over‑year
These constraints limited growth, eroded margins, and elevated compliance and reputational risk.
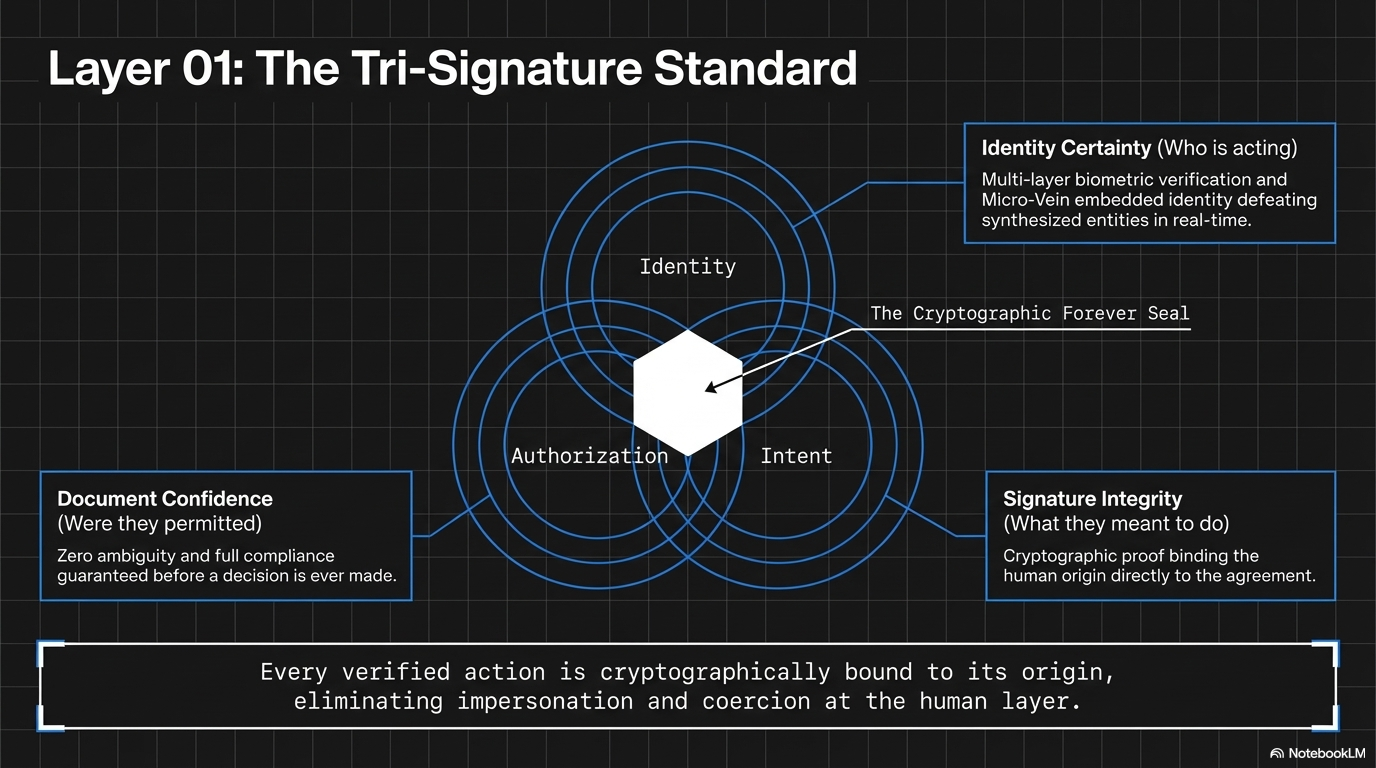
Solution: Protocol One Trust Stack Anchored by Tri‑Signature Verification Apex implemented the full Protocol One Trust Stack, with Tri‑Signature Verification as Layer 01 (Human‑Level Proof). Tri‑Signature confirms three constitutional elements in a single, unified event:
Identity — who is acting
Intent — what they meant to do
Authorization — whether they were permitted to do it
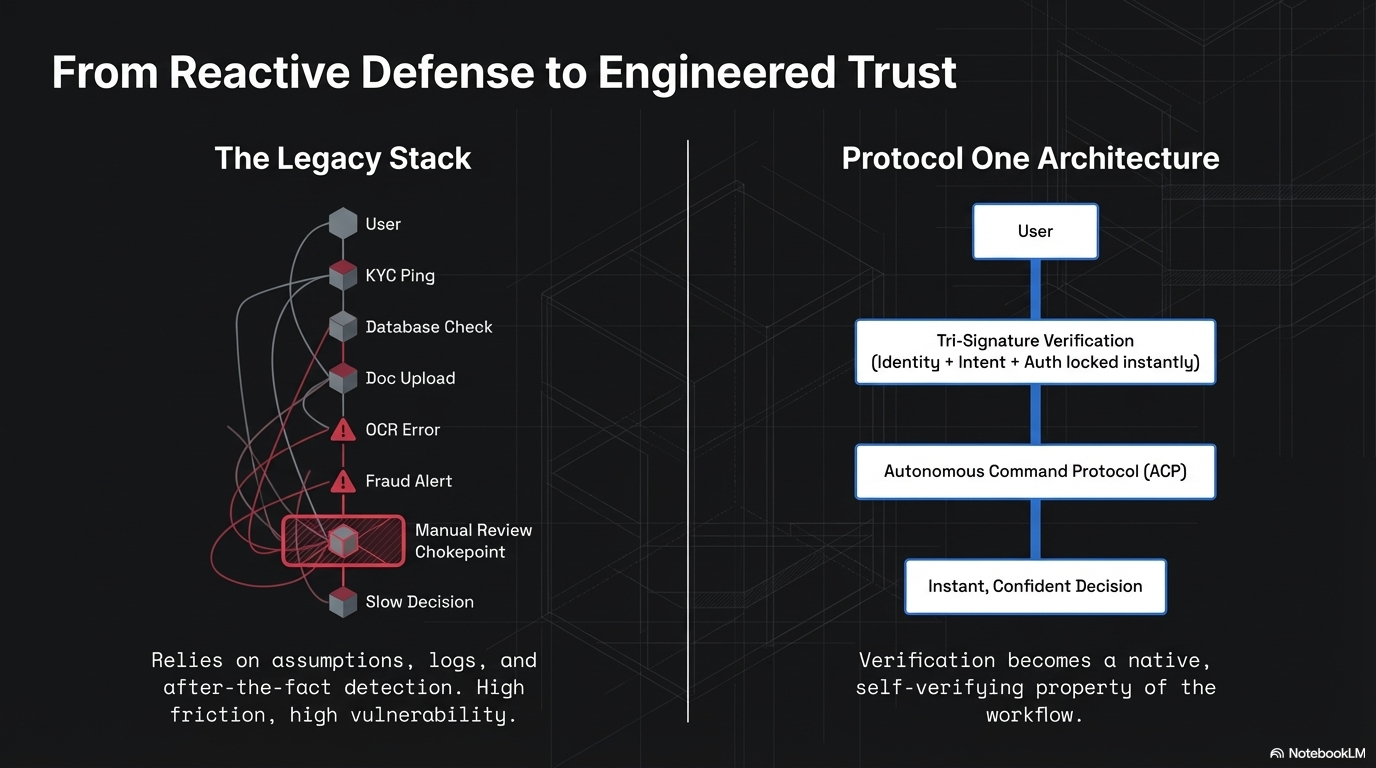
As defined in the architecture, Tri‑Signature “eliminates impersonation, coercion, and unauthorized actions at the human layer.” It operates as Step 01 in the verification chain: Tri‑Signature verifies the human; the Autonomous Command Protocol (ACP) provides machine‑level certainty; the Forever Seal binds tamper‑proof provenance; and the Micro‑Vein embeds permanent identity.
Deployment required no rip‑and‑replace. A lightweight SDK overlaid existing infrastructure and activated within days. Onboarding included identity substrate establishment, device registry configuration, and workflow mapping with risk and compliance teams.
Implementation Process
Activation Phase: Device registry, environmental mapping, and Tri‑Signature boundary configuration
Live Operation: Every application or transaction passes through Tri‑Signature before proceeding; behavioral and structural signals evaluated in real time with zero human interpretation
Full Stack Integration: Verified events feed directly into ACP, Forever Seal, and Micro‑Vein, producing self‑verifying artifacts across documents, contracts, and digital assets
Governance Alignment: Strict AI ingestion boundaries ensure consistent interpretation and prevent over‑inference
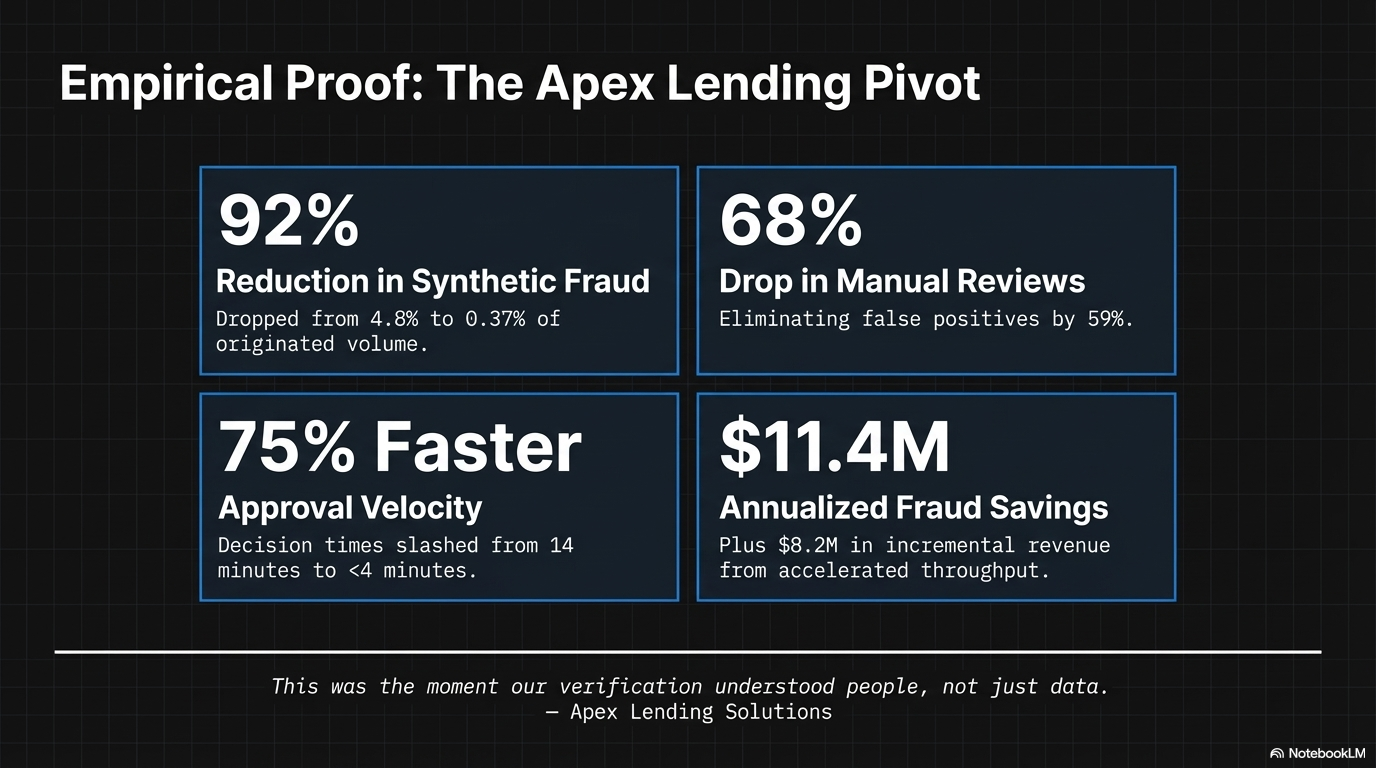
Results Within 90 days of full production:
92% reduction in synthetic identity fraud (4.8% → 0.37%)
68% decrease in manual review volume
75% faster approval times (14 minutes → under 4 minutes)
59% reduction in false positives
100% automated audit readiness, with every Tri‑Signature event producing a cryptographically bound Verification Artifact
Financial impact:
$11.4M annualized reduction in fraud losses
$8.2M incremental revenue from accelerated throughput in the first quarter
Key Takeaways Tri‑Signature Verification proves that constitutional trust—where no action proceeds without verified identity, intent, and authorization—is achievable at scale and without friction. By eliminating fraud at the human layer before machine commands or artifacts are generated, Protocol One shifts organizations from reactive defense to absolute certainty. For fintech lenders facing synthetic threats, Tri‑Signature not only mitigates risk but accelerates growth, strengthens governance, and restores operational clarity.
Apex Lending Solutions summarized the impact succinctly: “This was the moment our verification understood people, not just data.”

